Billions spent on cybersecurity, yet the front door is wide open.
A new analysis of the financial sector exposes a stark vulnerability in global banking infrastructure: despite record defense spending, only 30% of financial institutions have the governance and tech to stop advanced AI-driven deepfake attacks.
This isn’t a projection. It’s the hard reality from recent findings by bodies like ACCA Global and Regula. As generative AI tools become cheap and accessible, the barrier to entry for complex fraud has collapsed. The era of simple phishing is dead; the era of “digital injection” is here. Financial leaders can no longer ask if a deepfake will hit their institution. They have to ask a scarier question: Will our current security systems even notice?
The Integrity Gap: A Crisis of Confidence

That 30% readiness figure is a warning shot. It highlights a massive disconnect between how fast threats move and how slow defenses adapt.
Consider this: 70% of major banks have deployed biometric authentication—FaceID, voice recognition, the works. But most of these systems were built to catch human imposters wearing masks or holding up photos. They were not built to catch synthetic media.
Data from the World Economic Forum (WEF) and Deloitte puts a number on the problem. In 2025 alone, deepfake-related fraud attempts in North America surged by over 1,700%.
The core issue? Legacy “liveness detection”—asking a user to blink or turn their head—is obsolete. Attackers don’t need a physical camera anymore. They use real-time “digital injection” tools to feed pre-rendered or live-generated footage directly into the data stream. They bypass the lens entirely.
Financial institutions are waking up to a grim realization. Their “trust anchors”—the voice on the phone, the face on the video call—are now their primary attack vectors. Without an enterprise-wide roadmap for AI defense, the vast majority of banks are exposed to what experts call “weaponized familiarity.”
Anatomy of a $25 Million Heist
The threat went from theoretical to expensive in Hong Kong. This incident served as the industry’s wake-up call.
In a meticulously orchestrated scheme, a multinational firm lost $25.6 million (HK$200 million). How? An employee joined a video conference call where every other participant—including the supposed Chief Financial Officer—was a deepfake.
This wasn’t a technical hack of the bank’s servers. It was a reality hack. The attackers used publicly available footage to train AI models, synthesizing the voices and faces of the company’s leadership in real-time. This “CFO Trick” dismantled the long-held assumption that live video is proof of life.
The implications are severe. If a corporate finance officer can be duped by a synthetic video meeting, the verification standards for high-value wire transfers are broken. They must be rewritten from the ground up.
The Technology Deficit: Legacy vs. AI-Native Defense
Most banks are bringing a knife to a gunfight. The 70% of unready institutions largely rely on “Presentation Attack Detection” (PAD) level 1 or 2 standards. Against 2026-era generative models, PAD is ineffective.
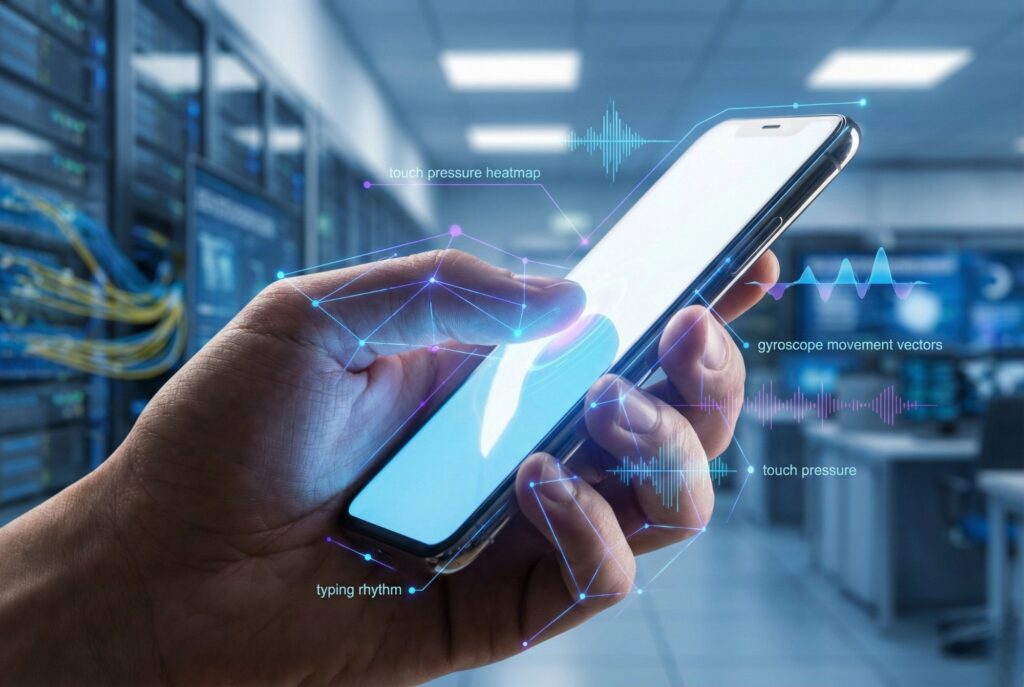
To join the 30% “ready” tier, institutions are pivoting. They are moving toward “Injection Attack Detection” and behavioral biometrics. It’s no longer about what the camera sees; it’s about where the data comes from.
The table below outlines the critical differences between the legacy systems most banks still use and the necessary AI-native defenses.
| Feature | Legacy Biometric Defense | AI-Native “Deepfake Defense” |
|---|---|---|
| Verification Method | Static Selfie or Passphrase | Passive Liveness & Behavioral Analysis |
| Primary Threat Model | Masks, Photos, Pre-recorded Video | Camera Injection, Real-time Face Swaps |
| Analysis Layer | Visual Spectrum only | Metadata + PRNU (Photo Response Non-Uniformity) |
| Response Time | Post-transaction audit | Real-time session termination |
| Failure Rate (vs AI) | High (>40% bypass rate) | Low (<1% bypass rate) |
| Cost to Implement | Low | High (requires GPU/Cloud infrastructure) |
Regulatory Pressure Mounts
Regulators aren’t waiting around.
The Monetary Authority of Singapore (MAS) and the US Financial Crimes Enforcement Network (FinCEN) have both issued circulars warning that deepfakes are now a systemic risk. The guidance is clear: banks must move beyond “something you are” (biometrics) to “how you act” (behavioral).
New compliance frameworks suggest that for high-risk transactions, a biometric match isn’t enough. It must be cross-referenced with device telemetry. Is the phone’s gyroscope moving consistent with a hand holding it? Is the video stream originating from a physical lens or a virtual camera driver?
The Path Forward
For the 70% of banks currently lagging, the path to readiness involves three urgent steps:
- Kill Single-Factor Biometrics: Face or voice alone can no longer authorize high-value transfers.
- Deploy Injection Detection: Security stacks must sit at the API level to detect when a camera feed has been hijacked by software.
- Verify the Verifier: Internal communication channels—like Zoom or Teams—must be treated as “zero trust” environments.
The gap between attacker capability and bank defense is widening. Closing it will require not just new software, but a philosophical shift. Financial institutions must redefine “identity” in an age where seeing is no longer believing.
